The Critical Difference™
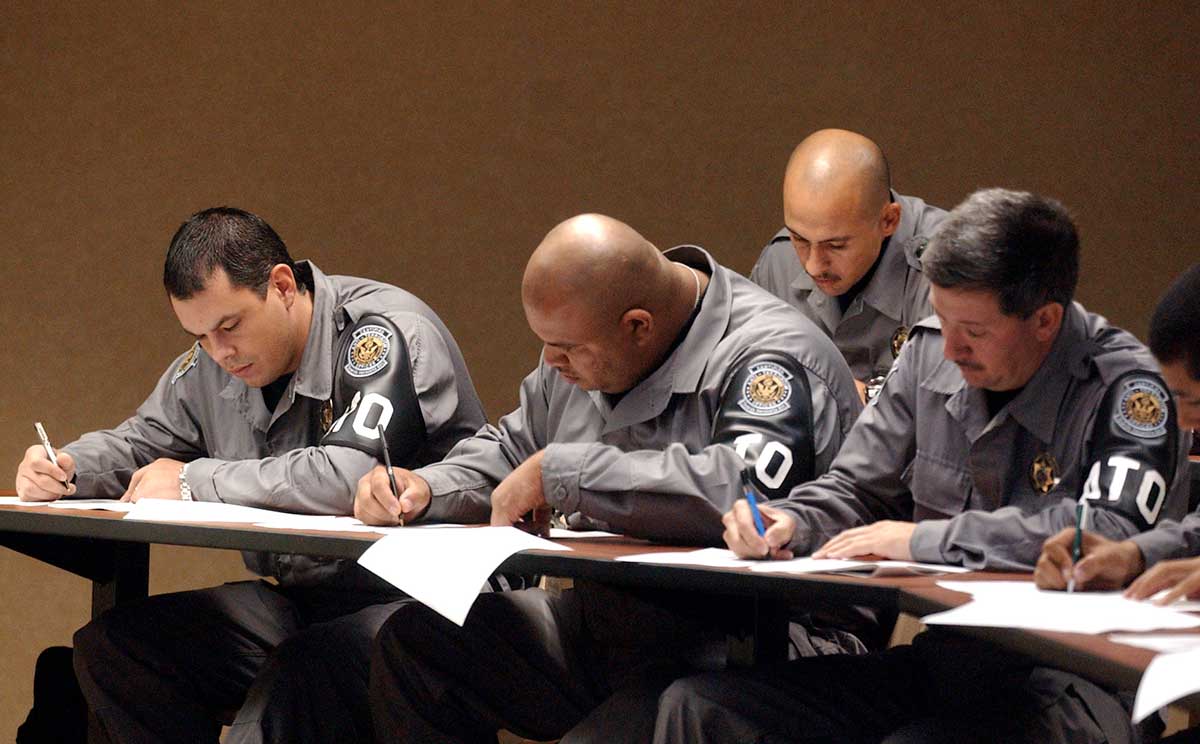
Anti-Terrorism Officers (ATOs)

Anti-Terrorism Officer Course: Now Online
Updated 10 May 2022 - The 40-hour Anti-Terrorism Officer (ATO) Course is now available on-demand as a distance learning course through our sister company, The S2 Safety & Intelligence Institute.
Click for more information.
The CIS Anti-Terrorism Officer (ATO) Program

As a source of security risk, terrorism is unique and the tactics and capabilities employed by terrorists require that security personnel receive specialized training, equipment, planning support, and tactical supervision. Historically, few security forces outside the government community are adequately prepared to prevent and respond to terrorist violence.
To address this need for security personnel with specialized anti-terrorist capabilities, Critical Intervention Services created the CIS Anti-Terrorism Officer program in 2004.
Anti-Terrorism Officers (ATOs) are armed security or law enforcement personnel that have been specially selected, trained, and equipped for employment in situations where terrorism is a critical risk.
Between 2004 and 2020, CIS provided Anti-Terrorism Officers as service for critical infrastructure clients in the Tampa Bay region. As the only security officer corps of its type in the United States, the program earned accolades from numerous U.S. government agencies for its comprehensive and performance-based design, summarized in words of the U.S. GAO as a “…model for critical infrastructure protection in America.”
The CIS Anti-Terrorism Officer (ATO) Program as a Worldwide Standard
Beyond the United States, the CIS ATO training program has been adopted by numerous government organizations and NGOs for training and preparing security personnel for this specialized mission. Some examples of organizations which have adopted the CIS Anti-Terrorism Officer program include the European Commission, European External Action Service, Organization for Security and Cooperation in Europe, and government ministries representing over a dozen nations worldwide. The program was also adopted as the basis for developing the Anti-Terrorism and Physical Security course for the Ministry of Interior of Iraq in 2010.
Since its inception, over 3,000 professionals worldwide have graduated the Anti-Terrorism Officer course developed by CIS.
Although the agency no longer provides armed ATO’s as a security officer service, CIS continues to assist organizations around the world in developing and preparing security forces for the mission of protecting people and assets against terrorist violence.
For information about our services as consultants and instructors on anti-terrorism issues, contact:
Craig Gundry, PSP, cATO
Vice President of Special Projects












The Words of Our Clients and Peers
Toll-free: (800) 247-6055 | Tampa Bay Area: (727) 461-9417 | Hillsborough: (813) 910-4247 | Orlando: (407) 420-7945

Critical Intervention Services
The Critical Difference™
Contact Us
The staff of CIS is dedicated to providing each client with the finest quality of protective services available.
Our commitment and dedication to professional, ethical, and protocol conscious service is our trademark.
Preserving, projecting, and protecting our clients’ image and interests is our business.
Copyright © 2020 Critical Intervention Services, Inc. ® Florida “A” License: A9900261 • Florida “B” License: B9200107
