The Critical Difference™
Technical Security Services
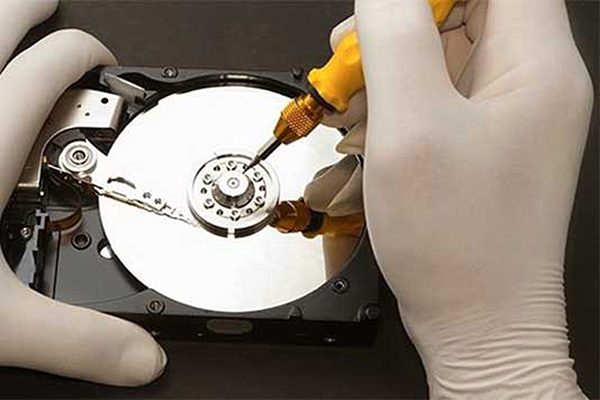
Digital Forensics & Data Recovery
In today’s paperless business world, destruction of evidence of impropriety and illicit computer activity can be as simple as pushing a delete key. Without the proper tools and expertise, retrieval of deleted data is often difficult if not impossible.
Our digital forensic technicians can assist companies in recovering deleted data and assessing illegitimate computer use. This service provides a critical advantage to companies during internal investigations, hostile terminations, and assessment of businesses during mergers and acquisitions.
Our staff of expert technicians use state-of-the-art methods for retrieval of data on storage devices, regardless of its deleted status. In many cases, our technicians can even recover data if storage devices have been physically damaged. Throughout the recovery process, our technicians use stringent protocols to ensure integrity in the duplication and handling of data devices and retrieval products to ensure that all collected evidence stands up to scrutiny by court of law.

IT Crisis Intervention & Auditing
In today’s era of technology-driven business, few employees have as much influence over the continuity of operations as the information technology staff. IT department employees often possess the “keys to the kingdom” with detailed knowledge of passwords, network vulnerabilities, and access to sensitive data.
In these situations, the hostile termination of a trusted IT employee can be exceptionally dangerous. If not handled properly, a disgruntled IT employee can cause significant loss by compromising the security of proprietary information and sabotaging network operations.
One solution to this problem is our IT Security & Response Team (IT/SRT). Our security experts can quickly evaluate your computer network and establish immediate safeguards to prevent compromise. The IT/SRT can then assess the network for indications of malevolent activity and establish monitoring controls to detect attempts at unauthorized intrusion and tampering. Once the situation is deescalated, the IT/SRT can transition control of the system back to your trusted IT department or to a new IT manager. As an additional layer of protection, our IT security experts can also establish a long-term program to audit network activities for signs of impropriety by permanent IT employees.
Technical Surveillance Countermeasures (TSCM)
Interception of communications by means of audio or video surveillance is one of the many methods used by hostile competitors and foreign governments to collect sensitive information from target entities.
As an aid in combating this threat, our government-trained TSCM technicians use state-of-the-art equipment and techniques to detect the presence of surveillance devices and the compromise of communications systems. These services can be used to ensure the integrity of offices, conference rooms, and company telephone/data systems. Our personnel can also provide on-site pre-event bug sweeps and spectrum monitoring services during critical meetings to ensure that your sensitive discussions remain confidential.

Contact Us
Contact us to discuss your unique needs by calling Tel. +01 (727) 461-9417 or by completing the following form:
The Words of Our Clients and Peers
Toll-free: (800) 247-6055 | Tampa Bay Area: (727) 461-9417 | Hillsborough: (813) 910-4247 | Orlando: (407) 420-7945

Critical Intervention Services
The Critical Difference™
Contact Us
The staff of CIS is dedicated to providing each client with the finest quality of protective services available.
Our commitment and dedication to professional, ethical, and protocol conscious service is our trademark.
Preserving, projecting, and protecting our clients’ image and interests is our business.
Copyright © 2026 Critical Intervention Services, Inc. ® Florida “A” License: A9900261 • Florida “B” License: B9200107
